It’s weird issue fixing week, one of my HomePod mini’s started playing up a while back and it basically was acting like the touch sensor was always “touched”. Before that it was randomly starting music every few minutes and stopping it, which was… a little cursed.
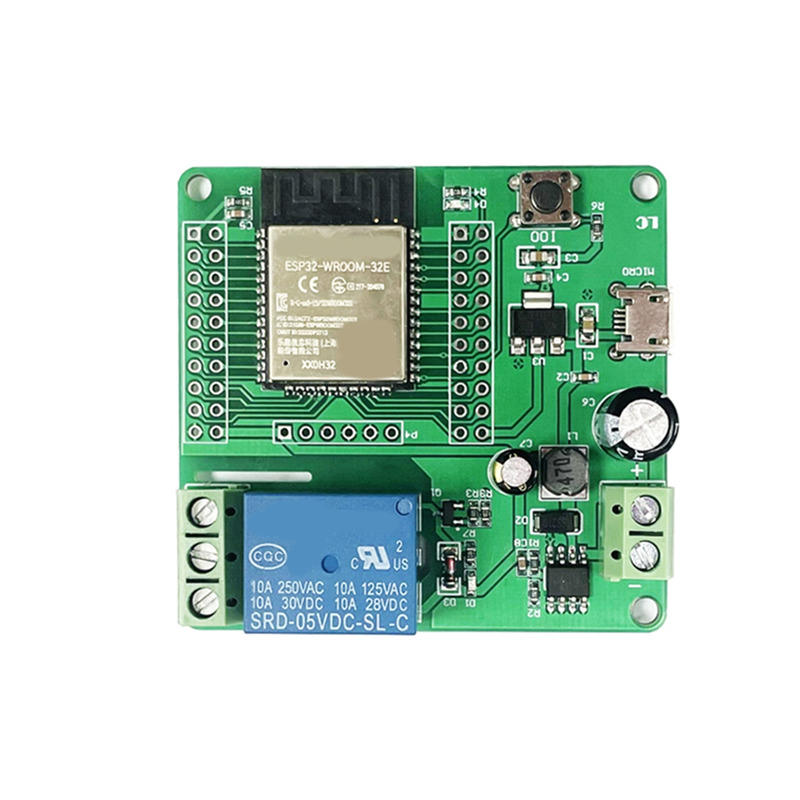
I think it might have gotten a weird voltage spike from the house power because the AC-DC power supply on one of my Sonoff smart switches on the same power board died around the same time. It worked with UART power, but just not from the wall power.
[Read More]